In December 2018, the so-called ‘encryption laws’ were passed, allowing law enforcement agencies to ask or compel technology or communication-based companies to assist with law enforcement investigations. These agencies have already started issuing notices and requests. Therefore, you should have a detailed internal plan when you do get a request or notice. This article will explain how your business can handle a request for access to encrypted data under the new encryption laws.
Encryption Laws Overview
The new encryption laws aim to crack down on serious crimes such as terrorist activity and child pornography. Law enforcement agencies such as the Australian Federal Police can issue certain requests or notices to anyone who is a “designated communications provider”.
That broad definition can include:
- hosting service providers;
- software developers;
- e-commerce stores; and
- software as a service (SaaS) providers.
You may receive one (or more) of these types of requests or notices, such as:
- TARs (technical assistance requests);
- TANs (technical assistance notices); or
- TCNs (technical capability notices).
What does the Request or Notice Involve?
The law enforcement agency can send the notice or request to a registered address or email address of your business. If you are a sole trader, you will directly receive the notice or request. Companies can receive the notice at their registered office.
Technical Assistance Requests
Complying with a TAR is voluntary. You may have to provide technical assistance in any way that the relevant agency believes will assist their investigation. You are not required to act at all if you receive a request, although you can choose to comply with the request.
Technical Assistance Notices
Complying with a TAN is compulsory. The law provides a list of activities that you must do if you receive the notice. The TAN will rely on the company’s existing features for law enforcement.
Technical Capability Notice
Complying with a TCN is also compulsory. A TCN is a legal step-up from a TAN, where law enforcement officials will ask you to build new features into your product so they can carry out their enforcement activities.
Continue reading this article below the formCall 1300 544 755 for urgent assistance.
Otherwise, complete this form, and we will contact you within one business day.
Who Can I Tell About the Request or Notice?
If your business receives a request or notice, you are not allowed to disclose that you have received one. You also cannot disclose the contents of the request or notice. Those restrictions apply to:
- businesses;
- employees of the business;
- contractors of the business; and
- employees of the contractors.
There are some exceptions to this rule.
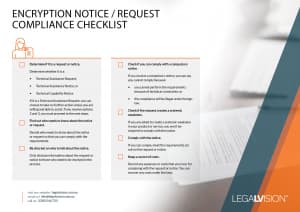
Internal Process Checklist
Complying with a request or notice can be an overwhelming experience, especially if you are a startup or small business with few resources. The checklist below provides an overview of the steps you can take to comply with your encryption law obligations.
Click here to view and download the checklist.
Key Takeaways
Law enforcement agencies have already issued requests or notices under the laws. You should know what you could be asked to provide as part of a specific notice or request. Be sure to educate your staff on these issues. If you have any specific concerns or would like assistance on how to comply, get in touch with LegalVision’s IT lawyers on 1300 544 755 or fill out the form on this page.
We appreciate your feedback! Request your free consultation now.