On this page
- 1. What is the Purpose of the Encryption Laws?
- 2. Who Will Be Affected by the Laws?
- 3. Who Sends the Request or Notice to the Business?
- 4. Who Receives the Notice or Request?
- 5. What Can The Notice or Request Ask You To Do?
- 6. How Do You Process the Request or Notice?
- 7. Can You Avoid Complying with the Laws?
- Key Takeaways
In December 2018, Australia passed the so-called ‘encryption laws’ which gave law enforcement and national security agencies the power to require industry assistance for the investigation of serious crimes. The laws have provoked a backlash among technology startups and small businesses, who fear that the laws will drive their business outside of Australia. This article will answer the frequently asked questions (FAQs) about Australia’s new encryption laws.
1. What is the Purpose of the Encryption Laws?
The encryption laws allow certain government agencies to compel or request assistance from businesses to investigate serious criminal activity, such as terrorism and child pornography. Law enforcement agencies have long expressed concern about their inability to catch potential criminals who use encrypted products or services.
Law enforcement agencies can request or compel businesses for assistance through one (or multiple) types of notices, which are a:
- TAR (technical assistance request);
- TAN (technical assistance notice); or
- TCN (technical capability notice).
At the time of writing, politicians have proposed amendments to the laws that may expand the use of the laws to anti-corruption agencies. Simultaneously, there are amendments to narrow the scope of the laws, such as specifying the definition of ‘systemic weakness’ in a product or service. This article will be updated if the Federal Parliament passes any future amendments to the encryption laws.
2. Who Will Be Affected by the Laws?
The laws affect anyone who is a “designated communications provider”. The definition is broad, covering any electronic service that serves Australian users, or a service that facilitates or supports the electronic services.
That could mean the laws affect a wide range of businesses, such as:
- hosting service providers;
- software developers;
- e-commerce stores; and
- software as a service (SaaS) providers, such as online providers of document storage and management.
The law also affects foreign companies who serve one or more Australian users.
Continue reading this article below the formCall 1300 544 755 for urgent assistance.
Otherwise, complete this form, and we will contact you within one business day.
3. Who Sends the Request or Notice to the Business?
You can receive requests or notices from various law enforcement agencies, such as:
- ASIO (Australian Security Intelligence Organisation);
- ASIS (Australian Secret Intelligence Service);
- ASD (Australian Signals Directorate); and
- the Australian Federal Police (or the police force of the relevant state or territory).
These agencies can send notices and requests as part of carrying out their function, such as ASIO carrying out surveillance on terrorist suspects. However, the notices can relate to serious matters like potential terrorism or child pornography. Additionally, agencies can use the notices to investigate criminal offences that are punishable by at least three years’ imprisonment, either in Australia or overseas.
Foreign law enforcement agencies can also request notices and requests to be issued on their behalf. The notice or request must relate to investigations of serious criminal offences and any enforcement action which occur overseas.
4. Who Receives the Notice or Request?
The relevant agencies will send the notice or request to a registered address or email address of the business. For companies, the notice will arrive at the registered company address, addressed to the company directors. Otherwise, sole traders will directly receive the notice.
If the laws apply to your business, you should develop internal procedures that ensure you correctly follow the procedure on complying with the encryption laws.
5. What Can The Notice or Request Ask You To Do?
There is little guidance as to what you could be asked to do under each type of request or notice. Law enforcement agencies may request your business to:
- supply customer data;
- create a new version of your software that enables or disables certain behaviour; or
- provide the government agency with administrator access to information hosted by you.
- remove electronic protection (such as encryption) from your products;
- provide technical information;
- ensure that the obtained information is in a particular format; and
- modify characteristics of a service that you provide.
6. How Do You Process the Request or Notice?
Whether you receive a notice or request, you are not allowed to disclose that you have received one. You also cannot disclose the contents of the request or the notice. One exception is where you can disclose the notice to your staff or relevant contractors if that disclosure helps you comply with the notice or request.
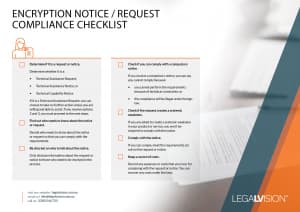
After receiving the notice or request, your next steps are to:
- determine whether you have received a TAR, TAN or TCN;
- find out who needs to know about the notice or request;
- disclose what is necessary to comply with notice or request;
- check if you are required to comply with the notice (if it is a TAN or TCN);
- check if the notice requires you to create a systemic weakness;
- comply with the notice, if you have followed the above steps and found no objections; and
- keep a record of costs.
You can download a full-size copy of the checklist below.
7. Can You Avoid Complying with the Laws?
The law is drafted broadly to cover anyone who provides electronic services to end users in Australia. If you want to avoid the laws, you have to avoid serving Australian customers. You could potentially restructure your business so that your Australian company serves Australian customers only. Therefore, your foreign companies can deal with any global customers without the potential need to comply with Australia’s encryption laws.
Key Takeaways
You may be one of many Australian businesses who provide electronic services to Australian users. Therefore, Australia’s encryption laws are likely to affect your business operations as well as the security of your product. If you must comply with the laws, ensure you have internal procedures in place that allow you to comply with the requirements. If you have any questions or need assistance on how your business can comply with the encryption laws, get in touch with LegalVision’s IT lawyers on 1300 544 755 or fill out the form on this page.
We appreciate your feedback! Request your free consultation now.











