On this page
Rebecca: Good morning, everyone, and welcome to our webinar, You’ve Been Hacked: Legal Steps and Duties After a Data Breach.
My name is Rebecca Wood. I am the Practice Group Leader of the Disputes team here at LegalVision, and I am looking very much forward to sharing some of my experience in dealing with these matters on a day-to-day basis.
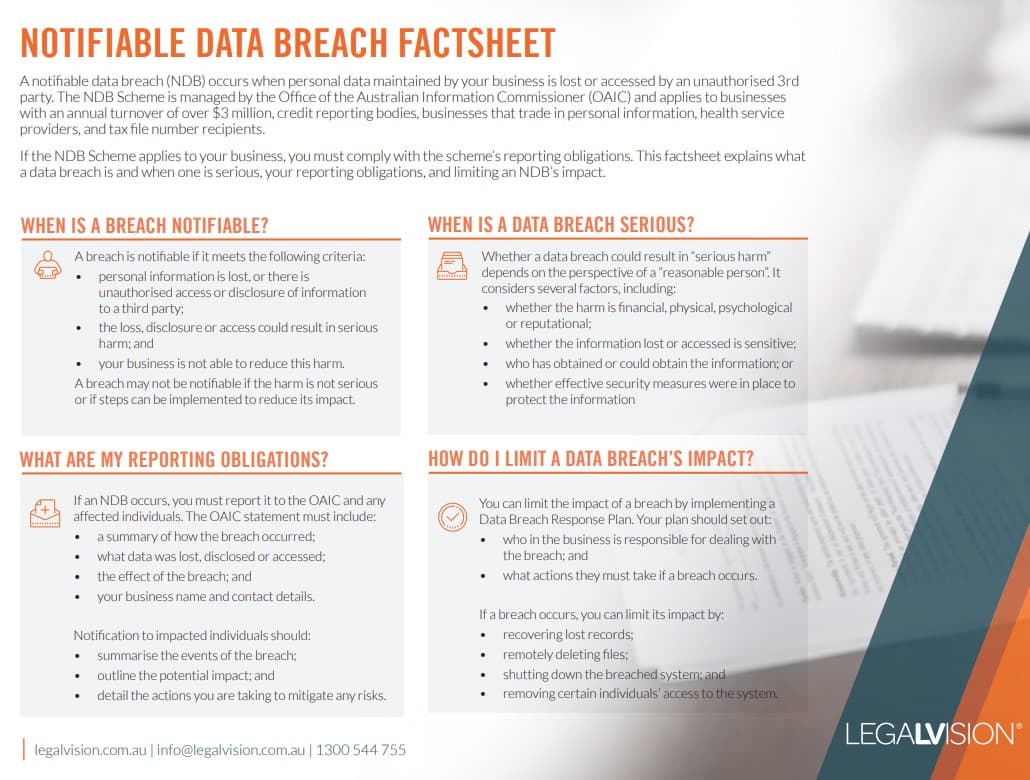
This factsheet explains what a data breach is and when one is serious, your reporting obligations, and limiting an NDB’s impact.
Agenda
Today, we are going to be discussing why data breaches matter and what the law requires you to do.
I am going to give you an overview of the Notifiable Data Breach Scheme and talk about what a data breach is. We will also look at what this looks like in practice, what to do when information is jointly held, and who is responsible.
In addition, we will cover the consequences of not getting it right, some mitigation strategies, and how to address third-party risk. I will then finish with my top tips and key takeaways, before we move into questions and answers.
Why Data Breaches Matter
As we are seeing, data breaches are no longer a rare or isolated incident. They are now becoming a routine business risk that every organisation needs to plan for.
The threat landscape has changed dramatically. Breaches are not just incidents that occur through sophisticated hackers, but often occur through human error, insider threats, and failures in basic information governance.
For in-house counsel and compliance teams, data breach preparedness is now a core legal function rather than just an IT issue. For business owners and operators, the question is no longer whether you will experience a breach, but whether you are ready to respond when you do.
Continue reading this article below the form
Call 1300 544 755 for urgent assistance.
Otherwise, complete this form, and we will contact you within one business day.
The Privacy Act and Who It Applies To
The Privacy Act is the primary federal legislation governing the handling of personal information in Australia. It contains 13 Australian Privacy Principles, or APPs, which are principle-based obligations regarding the use of personal information.
It applies to APP entities, which include organisations with an annual turnover over $3 million. Regardless of turnover, it also applies to private sector health service providers, credit reporting bodies and credit providers, tax file number recipients, businesses that trade in personal information, and businesses related to an APP entity.
Small businesses with an annual turnover of less than $3 million are generally exempt, although there are exceptions. The Act also extends to overseas activities of Australian entities with an Australian link.
The Notifiable Data Breach Scheme
The core obligation of the Notifiable Data Breach Scheme is to ensure that affected individuals are aware of a privacy breach that may apply to them, and that the OAIC is notified.
The primary purpose is to ensure that individuals can take proactive steps to protect their personal information, such as changing passwords, monitoring accounts, or placing credit bans before harm materialises.
The secondary purpose is to ensure accountability and build public trust in how organisations handle personal information.
The Current Data Breach Landscape
Data from the Office of the Australian Information Commissioner shows that 37% of data breaches are caused by human error. This is important, because many people assume breaches are caused by malicious attacks, when in fact they are often the result of everyday mistakes.
Another key insight is that many breaches affect only one individual. This highlights that even a small incident can still trigger legal obligations.
The types of personal information most commonly involved in breaches include contact and identity information. This means that even relatively basic data can give rise to a notifiable event.
What Is a Data Breach?
For a data breach to occur, three criteria must be satisfied. There must be an unauthorised disclosure of, access to, or loss of personal information. That breach must be likely to result in serious harm to one or more individuals, and the entity must have been unable to prevent that harm through remedial action.
“Likely” means more probable than not. Serious harm is not defined in the Act, but it can include physical, psychological, emotional, financial, or reputational harm.
The assessment is objective. It involves weighing the potential outcomes and determining what a reasonable person would conclude in those circumstances.
Responding to a Data Breach
The OAIC sets out a four-step approach to responding to a notifiable data breach.
The first step is containment. As soon as a breach is discovered or suspected, you must act immediately to limit further compromise. This may involve isolating systems, changing access credentials, recovering devices, or blocking unauthorised access. It is important not to destroy evidence during this process.
The second step is assessment. This involves determining whether serious harm is likely. Relevant factors include the sensitivity of the information, how the breach occurred, who accessed the data, and whether affected individuals are vulnerable. This assessment must be completed within 30 calendar days, which is a maximum timeframe.
The third step is remediation. If remedial action prevents serious harm, then the breach may not be notifiable. For example, if an email is sent to the wrong recipient but is confirmed to have been deleted without further disclosure, that may be sufficient.
The fourth step is notification. If the breach is notifiable, you must notify both affected individuals and the OAIC. The notification must include details of the breach, the types of information involved, and recommended steps individuals should take.
Jointly Held Information
Where personal information is jointly held by multiple entities, all parties have obligations under the scheme. However, only one party needs to notify, and compliance by one is taken to be compliance by all.
In practice, the entity with the most direct relationship with the affected individuals should take the lead. It is also important to address these responsibilities in contracts before a breach occurs.
Consequences of Non-Compliance
The OAIC has a broad range of enforcement powers, including investigations, enforceable undertakings, determinations, and civil penalty orders.
Compensation is typically awarded for non-economic loss, such as distress, anxiety, or humiliation. Economic loss may also be compensable where there is evidence of direct financial impact.
Reducing Risk
Organisations should focus on strong foundations. This includes complying with the APPs, minimising the personal information they collect, encrypting sensitive data, implementing access controls, and maintaining audit logs.
It is also essential to have a clear and up-to-date data breach response plan. This should include escalation procedures, reporting lines, and regular staff training.
Third-Party Risk
Contracts should clearly define what constitutes a data breach and set out notification obligations. Organisations should avoid clauses that allow long delays and ensure responsibilities are clearly allocated.
Key Takeaways
The Notifiable Data Breach Scheme applies to a wide range of organisations. Notification obligations can arise quickly, and the 30-day assessment period is a maximum, not a target.
Remediation can sometimes prevent notification obligations, but documentation is critical. How you respond to a breach is just as important as the breach itself.
A well-documented and regularly tested response plan is one of the most effective ways to reduce risk.
We appreciate your feedback! Request your free consultation now.












